Recorded Webinar
How Unification Removes Complexity from Vulnerability Management
In 2023, IT security is complex, but it does not have to be hard.
In previous webinars, we have discussed the need for Complete Asset Coverage in the face of the multitude of Attack Vectors that cybercriminals will use to get access to your organization.
But, as the number of attack vectors grows, so too does the administration required by IT teams. Security departments know they need to scan as broadly as possible for vulnerabilities across all asset types.
This can be very hard to manage. Multiple products, multiple asset silos, and multiple dashboards for reporting on various risks across your business - The average organization just doesn't have the resources to make this easy.
In this webinar, we will be discussing the solution - a Unified Vulnerability Management Platform. By consolidating all your assets within a single platform, you can eliminate the headaches associated with fragmented security tools and disjointed workflows.
Gone are the days of jumping back and forth between products and platforms, grappling with increased training requirements, and dealing with unnecessary complexity.
The benefits of unifying your Vulnerability Management methods include:
Join this webinar, where our experts will guide you through the world of Unified Vulnerability Management. We will teach you how to maximize your efforts while minimizing business-critical risks.
In previous webinars, we have discussed the need for Complete Asset Coverage in the face of the multitude of Attack Vectors that cybercriminals will use to get access to your organization.
But, as the number of attack vectors grows, so too does the administration required by IT teams. Security departments know they need to scan as broadly as possible for vulnerabilities across all asset types.
This can be very hard to manage. Multiple products, multiple asset silos, and multiple dashboards for reporting on various risks across your business - The average organization just doesn't have the resources to make this easy.
In this webinar, we will be discussing the solution - a Unified Vulnerability Management Platform. By consolidating all your assets within a single platform, you can eliminate the headaches associated with fragmented security tools and disjointed workflows.
Gone are the days of jumping back and forth between products and platforms, grappling with increased training requirements, and dealing with unnecessary complexity.
The benefits of unifying your Vulnerability Management methods include:
- Simplified Prioritization - stop comparing vulnerabilities across assets. A unified risk-scoring algorithm ensures that you always focus on the most high-risk vulnerabilities first, providing a clear roadmap for remediation.
- Enhanced Collaboration - break down silos within your IT security team. With a unified view, everyone works together seamlessly, leveraging collective knowledge and expertise to safeguard your organization.
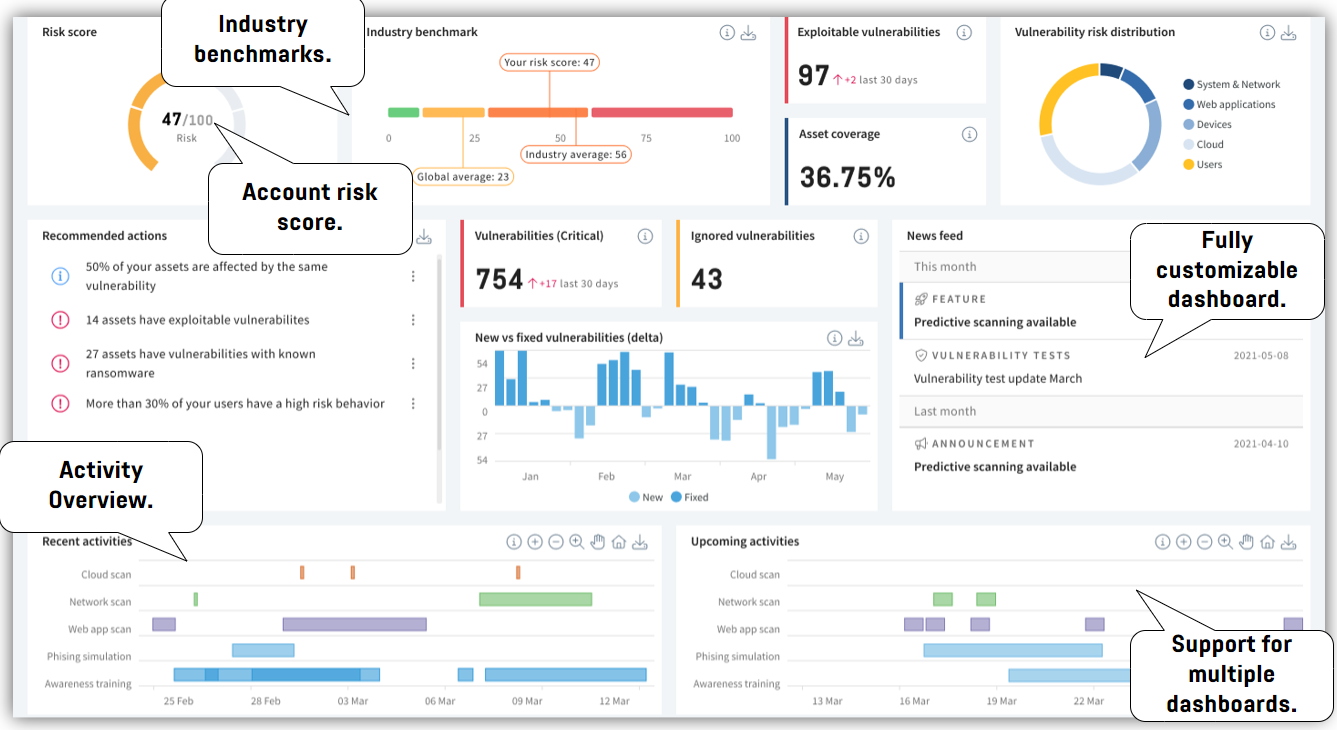
- Streamlined Reporting - No more aggregating information using multiple reporting tools and dashboards. Use unified reporting, consolidating all the data you need in one place for effortless analysis and decision-making.
- Cost Optimization - Say goodbye to vendor and product bloat. By harnessing the power of a single platform, you eliminate unnecessary costs, maximize efficiency, and make the most of economies of scale.
Join this webinar, where our experts will guide you through the world of Unified Vulnerability Management. We will teach you how to maximize your efforts while minimizing business-critical risks.
Register to Learn
- Improve your security posture with consistent trend analysis, enabling you to identify security gaps more quickly.
- Reduce complexity by implementing a cohesive cyber security strategy with consistent policies, procedures, training, and onboarding.
- Enhance your prioritization strategies with a unified risk-scoring algorithm, enabling you to allocate resources to the most critical vulnerabilities first.
- Simplify day-to-day management with a unified interface, saving time, reducing training costs, and enjoying comprehensive support.
- Foster better integration by eliminating silos and promoting seamless data exchange between your security tools.
- Unify your reporting efforts with all the information consolidated in one place, eliminating the need to switch between different reporting tools.
- Harness the power of economies of scale by scanning your entire attack surface within one platform, optimizing your security operations.


