General Data Protection Regulation (GDPR)
We are entitled to the fundamental right of integrity, which encompasses the right to privacy. Just as we lock our front doors to prevent unauthorized access, we have the right to decide who gains entry into our virtual spaces. The EU Charter of Fundamental Rights stipulates that everyone in the EU has the right to protect their personal data and get access to data collected and the right to have it rectified. But new technology has eroded this human right, and companies continuously collect data for their own purposes.
Consistency & Increased Security
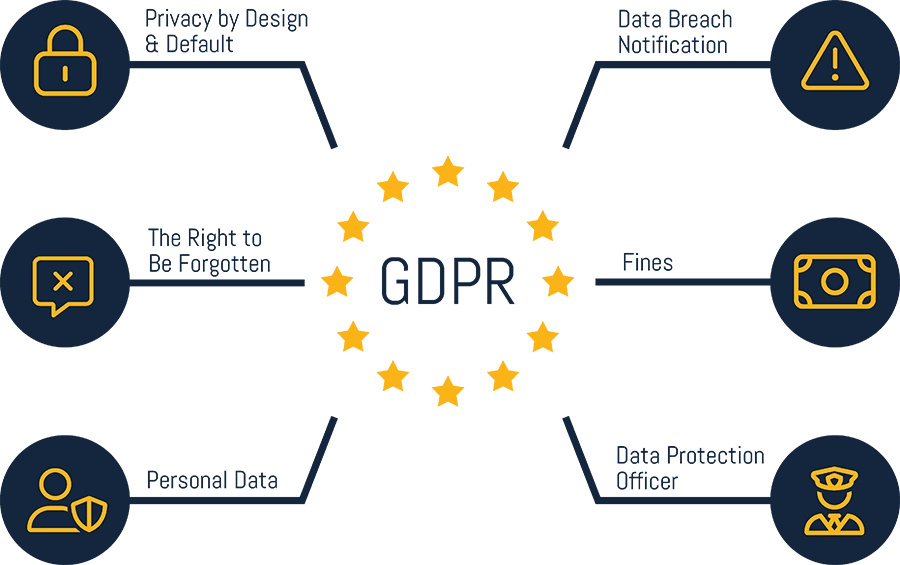
General Data Protection Regulation, or GDPR, came into force on 25 May 2018. GDPR aims to create coherence around the management of personal data within the EU. Because data protection is an essential part of GDPR, it has significantly impacted the importance of protecting personal data, especially from a cyber security perspective.
Continuous Evaluation of Cyber Security
Higher security demands and structured security management are necessary to protect personal data. Each organization must continuously ensure systems that handle or store personal data. Since most IT environments are a network of interconnected computers, servers, etc., organizations must ensure security throughout their entire IT environment.
Don't Wait Until It's Too Late. We'll Help You Comply with GDPR
We'll help you on your compliance journey.
The Seven Principles of GDPR
Lawfulness, Fairness, & Transparency
You may only process personal data if you meet the requirements of the law.
Integrity & Confidentiality
Personal information must be stored securely, not altered or stolen.
Data Minimization
You may only collect the information that is necessary to fulfill the purpose.
Accuracy
If you have personal information, you must keep it correct and up to date.
Storage Limitation
Data should not be kept longer than needed and should be deleted.
Purpose Limitation
You may only collect personal data for a specified purpose.
Accountability
You must be able to prove that you meet all these requirements.
Framework for Increased Security Audits
GDPR requires a combination of technology, processes, procedures, and people working together to guarantee personal data privacy. IT departments must establish security strategies and use them as a framework to prevent, monitor, and manage any data breaches. This includes developing policies and procedures to train employees to handle data correctly.
- Establish processes and systems to identify possible signs of intrusions or security irregularities and notify and report these instances.
- Implement preventive security systems such as firewalls and IDS (Intrusion Detection System).
- Monitor users with administrator privileges to detect discrepancies or deviant behaviors.
- Establish security policies that facilitate Continuous Monitoring of activities to detect irregularities or unauthorized access to personal data.
- Otherwise, ensure that your organization has sufficient protection for the organization’s network against threats such as unauthorized intrusion, removal, and sharing, as well as copying and attempting to copy information.

Safeguard Your Business from Cyberattacks
Extend Visibility
Know what you're up against. We can help you identify your IT system's weak points, categorize the assets that are vulnerable, and pinpoint the most likely threats. This knowledge will help you take action to protect your business proactively.
Prioritize Action
Identifying risks is just the first step; you need to act on them. We can help you develop a clear action plan that prioritizes your actions based on the level of threat, potential impact, and resources.
Communicate Risk
Don't keep cyber security risks a secret - communication is key. Get a clear view of your business's cyber risk with Holm Security. Our platform provides security executives and business leaders with centralized and business-aligned insights, including actionable insights into your overall cyber risk.

Ready to Navigate GDPR Compliance?
Book Your Consultation Meeting Today!
What You Need To Know About GDPR
Below are some of the most common questions and answers about GDPR, including links to more information.
What is the General Data Protection Regulation (GDPR)?
GDPR, or General Data Protection Regulation, is a regulation that applies to all EU member states. It replaced any previous local laws and was launched on May 25, 2018. The goal of this legislation is to create coherence around the management of personal data within the EU and increase security.
If a personal data breach occurs, the controller is required to notify the personal data breach supervisory authority within 72 hours of becoming aware of it.
In the event of non-compliance, penalties can be severe. The fines range from up to €10 million or 2% of annual global turnover (whichever is higher) to up to €20 million or 4% of annual global turnover (whichever is higher), depending on the specific articles of the regulation that have been breached.
Who Must Comply with GDPR?
If an organization handles personal data of individuals in the EU, they must comply with the GDPR. "Processing" refers to any activity involving data, such as collection, storage, transmission, and analysis. "Personal data" includes any information related to a person, such as their name, email address, IP address, and political affiliation. Compliance with GDPR is mandatory, regardless of an organization's location, if it processes personal data of people in the EU. This also applies to non-profit organizations.
Read more about who must comply with GDPR.
How Do I Comply with GDPR?
To comply with the GDPR, organizations need to take measures to safeguard the personal data they control. They should start by conducting a GDPR assessment to identify the personal data they have, where it is stored, and how it is protected. Additionally, they must follow the privacy principles set out in the GDPR, such as obtaining consent and enabling data portability. They may also need to appoint a Data Protection Officer and update their privacy notice, among other organizational steps.
Learn more from this GDPR checklist.
Which Companies Have Been Fined for Data Breaches, and What Were the Consequences?
In recent years, several companies have faced financial fines due to data breaches that compromised their customers' personal information.
Meta, the owner of Facebook, has been fined €1.2bn by Ireland's Data Protection Commission for mishandling user information. This is the largest penalty ever imposed for violating EU data protection regulations. As a result, Meta has also been instructed to suspend the transfer of user data from the EU to the US. The fine is equivalent to $1.3bn and is a record for breaching the General Data Protection Regulation (GDPR).
Another example is Capio St. Göran, a hospital whose information system was not adequately secured, allowing users full access to all patient data, including sensitive information. The hospital was fined for ignoring the principle of minimum access.
Finally, Mariotte also faced a significant financial penalty of €20.4 million due to a data breach that affected 339 million customers, 31 million of whom were EU residents. The lack of security measures in place allowed hackers to steal their personal information.
Latest news

5 ways to create a successful vulnerability management program
A successful vulnerability management program requires these 5 key components.

Coming up in 2025: Building the future of Next-Gen Vulnerability Management
Whether you manage thousands of endpoints or complex cloud infrastructure, our platform is evolving to meet your needs - with greater precision and flexibility than ever before.
