Safeguarding Your Business with Next-Gen Vulnerability Management
Your digital assets, ranging from property management systems to intricate infrastructures, are now as vital as your physical premises. Stop business-critical failures before they happen. Our Next-Gen Vulnerability Management Platform is designed to safeguard against cyber incidents and help you stay ahead of malicious actors. Don't let cyber threats hold you back.
Addressing Key Cyber Security Challenges
Phishing
The human element remains one of the most significant vulnerabilities in the real estate industry. Phishing attacks can target agents, property managers, or office staff to gain unauthorized access to property listings, client information, or transaction details. Ongoing education and training on preventing cyber threats is the best approach.
Supply Chain
The real estate industry is deeply interconnected with intricate property and investment networks. An issue with one entity can have cascading effects on others. Contractors or third-party service providers with inadequate cyber security measures can introduce vulnerabilities, making the entire property and investment chain susceptible.
Data Protection
Real estate transactions are more than just the exchange of property; they encompass a wealth of sensitive information, spanning from personal identities and contact details to intricate financial records and legally binding contractual specifics. A breach not only undermines the trust but also poses substantial financial and legal risks. Prioritizing data protection in real estate is both an ethical obligation and a critical business imperative.
GDPR Compliance Made Simple
With Holm Security, you can get a comprehensive assessment of vulnerabilities across your entire attack surface. Our solution can help your security team to efficiently reduce risks. Identify and safeguard systems that store and use sensitive data, preventing GDPR fines.
-
Prioritize Systems Handling Personal Data
Tag specific systems that process personal data as more important than other systems, amplifying the risk score of the asset and ensuring that the vulnerabilities found on these assets are prioritized for remediation. -
Keep Tabs on the Remediation Progress
Integrate with ticketing solutions like JIRA and ServiceNow to seamlessly fold remediation into your IT team’s existing workflow and ensure SLAs are met and GDPR systems are patched in a timely manner.

Start Your Compliance Journey Today
Try Our Platform for Free!
Empower Your Security Team
& Maximize Efforts
Holm Security delivers the broadest coverage and most thorough assessment of vulnerabilities across your entire attack surface. By leveraging our solution, your security resources can make a greater impact on risk reduction with minimal effort.
-
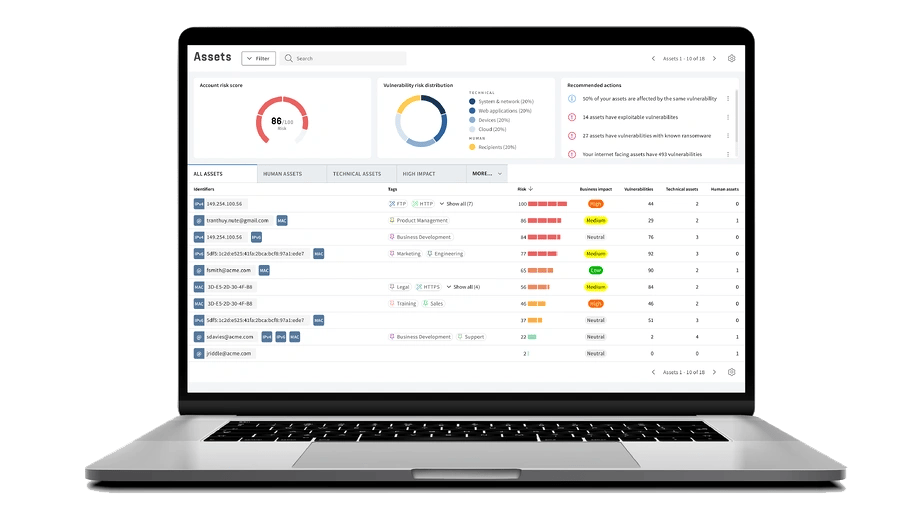
See Your Entire Attack Surface
Gain precise comprehension of all assets and vulnerabilities across your entire attack surface. This includes dynamic assets such as cloud-based banking software, remote devices and mobile banking apps that can be located anywhere and often fall outside the scope of traditional VM tools. With increased visibility, you can prioritize mitigation efforts and guarantee comprehensive protection. -
Transform Your Organization's Cyber Defense
Don't waste your time on vulnerabilities that don't pose a real threat. Our Unified Vulnerabilities view lets you track all risks in one place, including network, web, device, and phishing recipients. The new threat score prioritizes vulnerabilities for technical and human assets, making risk management easier.
Get A Complete Picture of Your Cyber Security Defense
Detect
Scan every potential entry point for attackers. Efficiently monitor and manage all of your systems, applications, endpoints, and employees.
Assess
Up your security game with fast and accurate scans, and prioritize the vulnerabilities that truly put you at risk from the ones that don’t.
Remediate
Cut down on unnecessary headaches with straightforward risk in real-time right from your dashboard. Measure and communicate progress effectively.
See For Yourself
Try Our Platform for Free Today!
Why Choose Our Vulnerability Management Solution?
Industry Expertise
We specialize in serving the real estate sector, and understanding the specific challenges and risks you face. Our solution is designed to tackle the vulnerabilities inherent in your industry.
Minimal Disruption with Maximum Protection
Our solution is implemented seamlessly into your existing infrastructure, providing robust protection without interrupting your exisiting processes.
Comprehensive Threat Detection
Our comprehensive platform provides exceptional visibility and insight, encompassing all assets, technical and human. Maximize your efforts and reduce business-critical risks with the least amount of effort.

















Latest news

5 ways to create a successful vulnerability management program
A successful vulnerability management program requires these 5 key components.

Coming up in 2025: Building the future of Next-Gen Vulnerability Management
Whether you manage thousands of endpoints or complex cloud infrastructure, our platform is evolving to meet your needs - with greater precision and flexibility than ever before.

