Navigating Safe Routes with
Next-Gen Vulnerability Management
In an era where transportation is a prime cyber-attack target, the stakes extend beyond data protection— they encompass the preservation of human life and the sustainment of unwavering public confidence. Every lingering vulnerability is an invitation to adversaries, from solitary hackers to advanced state-backed entities. Elevate your defense and guarantee a secure operational environment with our Next-Gen Vulnerability Management Platform.
Addressing Key Cyber Security Challenges for the Transport Sector
Ransomware Attacks
Limited Security Investment
Supply Chain Vulnerability
Employee Training
A strong defense isn't solely about advanced tools. Without proper training and awareness, employees can inadvertently become the weakest link, susceptible to manipulative tactics like phishing or neglecting cyber hygiene best practices.
.


Get Ready for NIS2
Within the complex web of modern infrastructure, transportation – spanning urban transit, rural roadways, and inter-regional air travel – stands out as an integral component underpinning both society and our global economy. The forthcoming NIS2 directive categorically recognizes the transport sector as vital. We'll help you adhere to the NIS2 requirements.
-
Unleash the Power of Risk Assessment
Prioritize security gaps and address new risks continuously to stay ahead of cyber threats. Our platform offers incident reporting for incidents and vulnerabilities, allowing you to monitor your security and proactively identify trends.
-
Ensure Business Continuity
Our platform enables you to easily identify vulnerabilities, minimize risk, and maintain compliance with just a few clicks. With our help, you can navigate the complexities of NIS compliance with ease, leaving you free to focus on what really matters - growing your business.

GDPR Compliance Made Simple
With Holm Security, you can get a comprehensive assessment of vulnerabilities across your entire attack surface. Our solution can help your security team to efficiently reduce risks. Identify and safeguard systems that store and use sensitive data, preventing GDPR fines.
-
Prioritize Systems Handling Personal Data
Tag specific systems that process personal data as more important than other systems, amplifying the risk score of the asset and ensuring that the vulnerabilities found on these assets are prioritized for remediation.
-
Keep Tabs on the Remediation Progress
Integrate with ticketing solutions like JIRA and ServiceNow to seamlessly fold remediation into your IT team’s existing workflow and ensure SLAs are met, and GDPR systems are patched in a timely manner.

Start Your NIS2 Compliance Journey
Try Our Platform for Free Today!
Empower Your Security Team
& Maximize Efforts
Holm Security delivers the broadest coverage and most thorough assessment of vulnerabilities across your entire attack surface. By leveraging our solution, your security resources can make a greater impact on risk reduction with minimal effort.
-
See Your Entire Attack Surface
Gain precise comprehension of all assets and vulnerabilities across your entire attack surface. This includes dynamic assets such as smart traffic management systems, fleet vehicles, and transportation mobile apps that can be located anywhere and often fall outside the scope of traditional VM tools. With increased visibility, you can prioritize mitigation efforts and guarantee comprehensive protection. -
Transform Your Organization's Cyber Defense
Don't waste your time on vulnerabilities that don't pose a real threat. Our Unified Vulnerabilities view lets you track all risks in one place, including network, web, device, and phishing recipients. The new threat score prioritizes vulnerabilities for technical and human assets, making risk management easier.
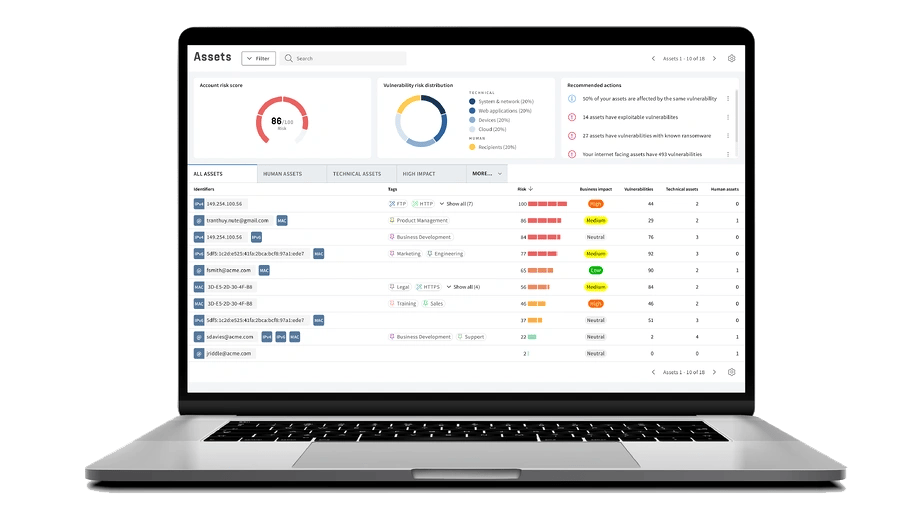
Get A Complete Picture of Your Cyber Security Defense
Detect
Scan every potential entry point for attackers. Efficiently monitor and manage all of your systems, applications, endpoints, and employees.
Assess
Up your security game with fast and accurate scans, and prioritize the vulnerabilities that truly put you at risk from the ones that don’t.
Remediate
Cut down on unnecessary headaches with straightforward risk in real-time right from your dashboard. Measure and communicate progress effectively.
See For Yourself
Try Our Platform for Free Today!
Why Choose Our Vulnerability Management Solution?
Industry Expertise
Our solution is designed to tackle the security challenges inherent in your industry, providing a robust shield against both current and emerging threats.
Minimal Disruption with Maximum Protection
Our solution is implemented seamlessly into your existing infrastructure, providing robust protection without interrupting your day-to-day business operations.
Comprehensive Threat Detection
Our comprehensive platform provides exceptional visibility and insight, encompassing all assets, technical and human. Maximize your efforts and reduce business-critical risks with the least amount of effort.

















Latest news

5 ways to create a successful vulnerability management program
A successful vulnerability management program requires these 5 key components.

Coming up in 2025: Building the future of Next-Gen Vulnerability Management
Whether you manage thousands of endpoints or complex cloud infrastructure, our platform is evolving to meet your needs - with greater precision and flexibility than ever before.

