Why manufacturing companies are in need of Next-Gen Vulnerability Management
Next-Gen Vulnerability Management is how Nolato scans its system to understand what a threat actor might see, allows its multiple plants to identify their specific vulnerabilities and related tasks, and extends the lifespan of their products.
Phishing Simulation & Awareness Training
Read the full transcript
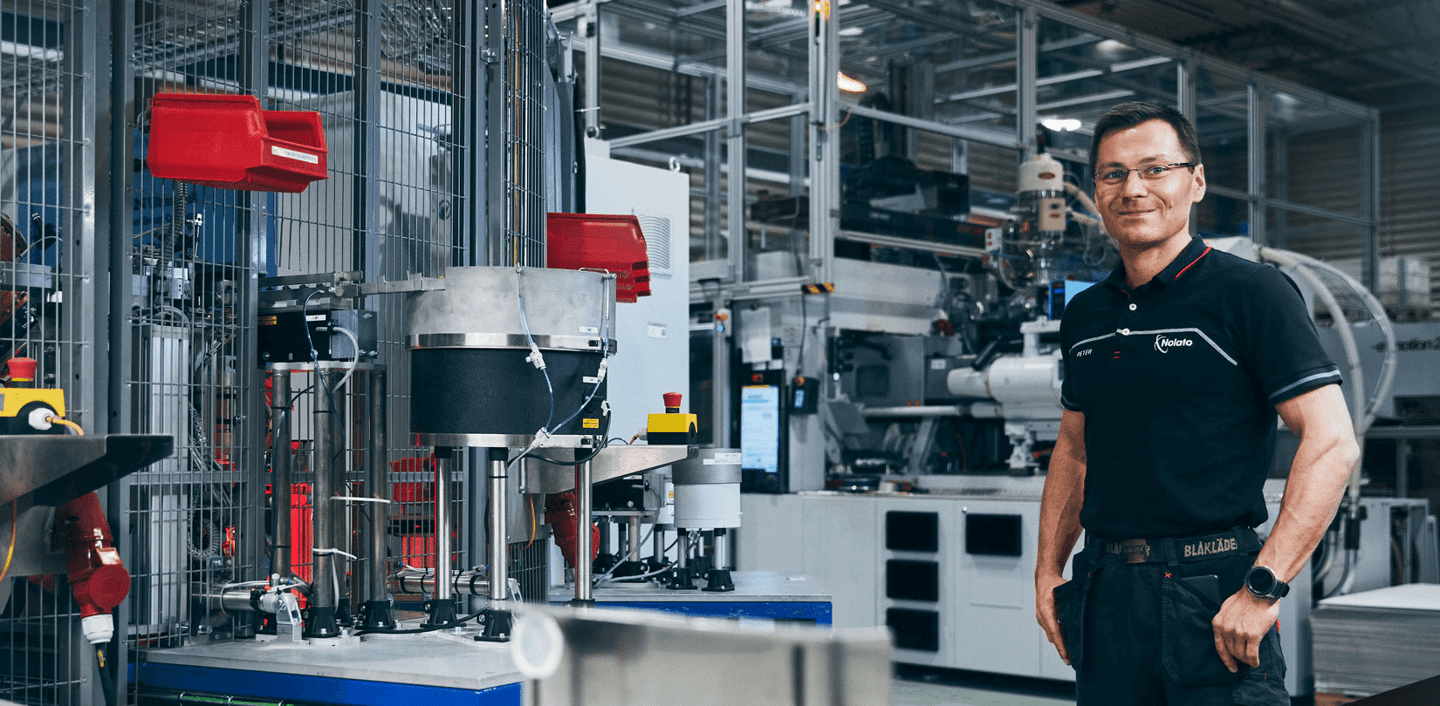
Nolato makes components for multiple industries in various different polymers, plastic, liquid silicone, also just plain rubber. I'm the IT Manager for Nolato GW. We have five different facilities in North America and I'm responsible for those as well as one in China. A big part of what I do is coordinating IT efforts with all those different plants, making sure not only that vulnerabilities are there but also that our project management is getting done appropriately.
In manufacturing, cost is very, very important to us and keeping our cost down. A lot of times that means that we have slightly older equipment so having a good vulnerability program helps us to extend the life of our products but we also need to do that keeping our manpower to a minimum, keeping everything efficient and innovating where we can.
We were looking for a software product or system that would allow us to get the information to all our different teams to allow them to act on what vulnerabilities we find in the system. No system is 100% perfect so for us it's very important to have that transparency. Holm Security was able to do that.
We were able to configure in a way so that each plant is able to go in and see specifically what their tasks are, what vulnerabilities are found, but yet we can also look at it from a global scale and see how the company is doing altogether. The threat environment is changing on a daily basis and having a system like Holm Security it allows us to see what the attacker or the bad actor might see if they get into our network. It shows us, without elevated privileges, what they can see and that bad actor they're going to get in, take over a benign device, and use that as a base of operations to slowly work their way up to more substantial devices. That could result in a loss of our ability to deliver our product to our consumers.
We chose to work with Holm Security because it was a simple solution - we could get it up and running fast. We actually had a testbed already running and spread that out so that all the IT teams could use it. We were able to do that in a matter of weeks. They also have both agentless and agent-based vulnerability scanning and what that means is you can see both what the threat actor might have access to without access to systems but also with the agent-based, if they do get into a system and compromise it, what are they going to see from the inside of that system that they can then use to attack our network even further? Another strength is the ability to tag things based on location or IP address allows us to very quickly organize the reports so that they are usable by all our staff.
Ready to accelerate your cyber security?
More case studies

Enhancing healthcare security with seamless vulnerability management
In the rapidly evolving field of healthcare, maintaining a robust security posture is paramount. For Amphia Ziekenhuis, a leading healthcare provider, vulnerability management became a crucial requirement to safeguard their infrastructure. In this case study, we explore how Holm Security's Next-Gen Vulnerability Management Platform (VMP) helped Amphia Ziekenhuis overcome their security challenges, gain valuable insights, and establish a proactive approach to vulnerability management.
Read more

Adding value with vulnerability management
Before using Holm Security VMP, we always wondered if we were safe. The platform gives us the insights and reassurance that we need. We are pleased that we found a platform that offers us great functionality for a reasonable price.
Read more
