The drawbacks of traditional vulnerability management
Traditional vulnerability management is the process of identifying, assessing, and addressing vulnerabilities in an organization's networks, systems, and applications. It typically includes the following steps:
-
Discovery
Identifying all assets, systems, and applications within an organization's network.
-
Scanning
Using software tools to scan the identified assets, systems, and applications for known vulnerabilities.
-
Assessment
Assessing the security posture of each asset, system, and application and identifying potential vulnerabilities or attack vectors.
-
Prioritization
Prioritizing vulnerabilities based on the potential impact on an organization and the likelihood of a successful exploit.
-
Remediation
Implementing security controls and remediation measures to address identified vulnerabilities or attack vectors.
-
Verification
Verifying that vulnerabilities have been successfully mitigated and that security controls are working as intended.
-
Reporting
Generating reports that provide visibility into the overall security posture of an organization.
Traditional vulnerability management was and still is considered a cornerstone of an organization's overall cyber security strategy. It enables organizations to identify and address security risks across their technical assets before cybercriminals can exploit them.
It also helps organizations reduce the risk of data breaches, compliance violations, and financial losses from cyberattacks. However, traditional vulnerability management can be time-consuming and resource intensive. The most glaring weakness is that it only covers some of the attack vectors that cybercriminals can exploit, missing out on essential attack vectors that cover your weakest link – your human assets, in other words, your employees.
Another area of weakness is that traditional vulnerability management solutions in the market today, like system and network vulnerability scanning, or web application vulnerability scanning, are siloed. Separate products that cannot share information or resources with each other, leading to inefficiencies and a lack of coordination. This can result in increased costs and reduced productivity. More importantly, it leads to data silos, where data cannot be shared or integrated, making it challenging to present business-relevant insights that are required to make informed decisions.
Revolutionizing vulnerability management with a next-gen approach
Next-Gen Vulnerability Management is a more efficient and modern approach to identifying and addressing vulnerabilities in an organization's networks, systems, applications, and employees of the organization.
It builds upon traditional vulnerability management when it comes to the process; however, it expands the attack vector coverage to include more technical assets, such as your cloud assets and attack vectors that are targeting your employees - your human assets.
In addition, Next-Gen Vulnerability Management presents not only a vulnerability report. It presents a business risk assessment showing how each security weakness could harm the business.
The following four pillars are what make up the foundation of Next-Gen Vulnerability Management:
- Extended attack vector coverage - Cover every corner of your IT infrastructure.
- True unification – A single view for all risks for efficient prioritization and remediation.
- Smart threat intelligence – Modern telemetry and AI enriching vulnerability data.
- Attack Surface Management (ASM) – Stay up to date with your attack surface to make sure it's fully covered.

Image: Pillars of Next-Gen Vulnerability Management
Extending attack vector coverage: The key to measuring & improving organizational cyber security
Attack vector coverage refers to the extent to which a system or network is protected against potential attack methods or entry points across the organization’s entire attack surface. It measures how well security controls can detect and prevent unauthorized access, exploitation, or compromise.
This includes external and internal attack vectors, such as network vulnerabilities, software bugs, and social engineering tactics that mainly exploit the employees’ cyber security knowledge of the organization.
The most crucial aspect of any attack vector coverage is the extent of coverage for maintaining the security and integrity of systems, data, and users. The more attack vectors you cover, the more knowledge you will have of how safe your business is from risks.
Next-Gen Vulnerability Management will extend such attack vector coverage to include all of your technical assets, including cloud, APIs, IoT, and OT/SCADA ensuring that both local software patching and misconfigurations in your cloud or internet-facing application security checks and your human assets are protected against phishing and ransomware, to name a few.
Creating a holistic approach to cyber security: The power of true unification
In the context of cyber security, true unification refers to creating a comprehensive security framework, a business risk scoring system, that can identify and prioritize all types of cyberattacks and threats. This is achieved by integrating various threat types into a unified system and then scoring such threats individually and in unison, resulting in threat intelligence that can illustrate the potential impact across the business.
The goal of true unification is to provide a complete and holistic approach to cyber security rather than relying on multiple, disparate solutions that will not be able to present the full potential impact across the whole of the business. This will enable organizations to coordinate their security efforts better and respond more effectively to cyber threats, all in one single view.
It is important to note that true unification in cyber security was, until recently, a challenging goal. However, with Next-Gen Vulnerability Management now covering several multiple security functions and technologies into a single, unified platform, this goal has become a reality.
Smart threat intelligence streamlining vulnerability prioritization
The digital realm is increasing its attack surface. As the number of attack vectors soars, organizations grapple with prioritizing vulnerabilities across diverse products and platforms. A significant setback is siloed systems, which often operate in isolation lacking seamless communication.
In addition to the typical CVSS score and its severity ratings (low, medium, high, and critical), the Unified Risk Score provides a range of 0 to 100 to simplify the process of ranking vulnerabilities across various systems, including computers, servers, cloud infrastructures, and users.
As part of Next-Gen Vulnerability Management, the attack vectors that target human assets are an integral part of the attack vector coverage and contribute to the computation of business risk scoring. This way, you get a total understanding of how any potential exploits of any of your assets, regardless of technical or human nature, and how much such could have a negative impact on your business.
What sets the Unified Risk Score apart is its integrative nature. It consolidates vulnerabilities from diverse sources while also accounting for varying properties and threat intel facets, including:
- Known exploits
- Ransomware threats
- Public exposure level
- Impact scope: Number of assets at risk
Attack Surface Management: Uncovering hidden cyber threats
As part of Next-Gen Vulnerability management, Attack Surface Management (ASM) identifies, assesses, and mitigates potential vulnerabilities and attack vectors within an organization's networks, systems, applications, and users. The goal of ASM is to reduce the overall attack surface of an organization by identifying and eliminating unnecessary or unsecured access points and implementing security controls that can detect and prevent cyberattacks.
Attack Surface Management is built upon the well-established and proven traditional vulnerability management process, as explained above.
ASM, as part of Next-Gen Vulnerability Management, includes the following steps:
-
Discovery
Identifying all assets, including systems and applications within an organization's network.
-
Analysis
Assessing the security posture of each asset, system, application, and user and identifying potential vulnerabilities or attack vectors.
-
Mitigation
Implementing security controls and remediation measures to address identified vulnerabilities or attack vectors.
-
Identify new threats
Continuously scans the entire attack surface for new vulnerabilities or changes in security posture and automatically identifies new threats to the business.
ASM is an essential aspect of an organization's overall cyber security strategy and integral to Next-Gen Vulnerability Management. It enables organizations to identify and address potential security weaknesses before cybercriminals can exploit them. It also helps organizations reduce the risk of data breaches, compliance violations, and financial losses from cyberattacks to lower overall business risks.
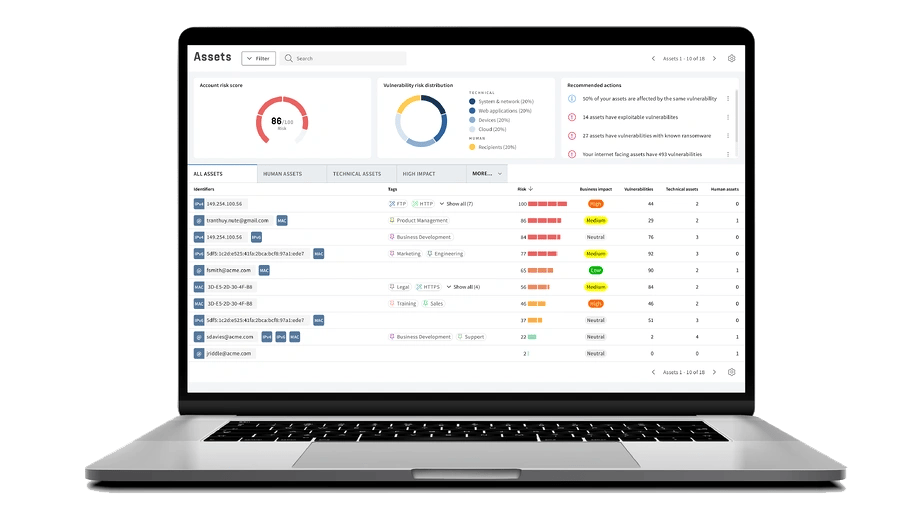
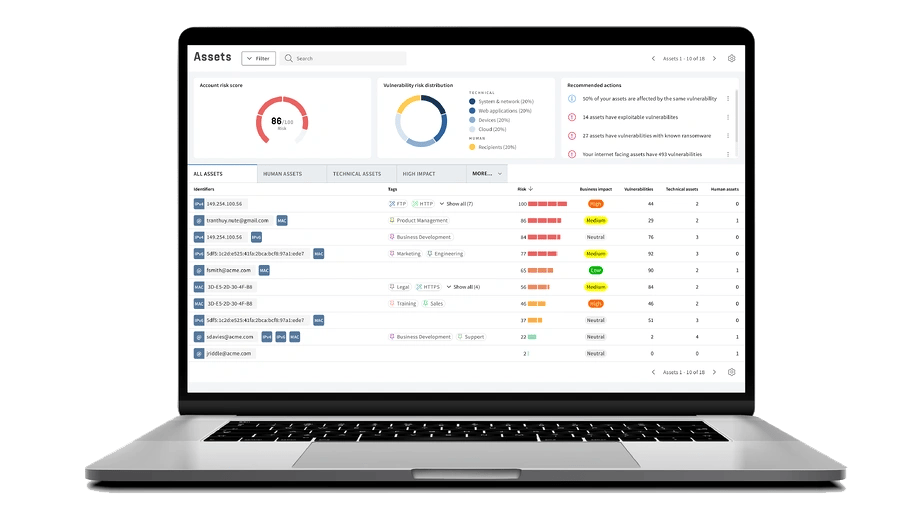 Image: Unified View of Assets
Image: Unified View of Assets
Conclusion
Traditional Vulnerability Management is no longer enough to mitigate business risks. Next-Gen Vulnerable Management is a more advanced approach to identifying and addressing potential risks to your business. Until recently, true unification in cyber security was a challenging goal, a dream, but it can now be realized with Next-Gen Vulnerability Management.
Key takeaway
The article discusses the limitations of traditional vulnerability management in protecting against business risks and suggests that Next-Gen Vulnerability Management is a more efficient and modern approach. Next-Gen Vulnerability Management expands on traditional vulnerability management by covering more attack vectors and assets, such as cloud assets and human assets (employees). It also includes a business risk assessment showing how each security weakness could harm the business. The four pillars of Next-Gen Vulnerability Management are extended attack vector coverage, true unification, smart threat intelligence, and attack surface management (ASM). The article highlights the importance of extended attack vector coverage in measuring and improving organizational cyber security and the power of true unification in creating a holistic approach to cyber security.