Efficiently Minimize Risk in Modern Web Applications
Find vulnerabilities, such as OWASP Top 10, in your websites, web apps, and APIs.
Find Weaknesses Where You Are the Most Vulnerable
Automated and continuous scanning of web applications detects vulnerabilities related to bad code, misconfigured systems, weak passwords, and exposed system information and personal data.
Complete Set of Tools
Providing all the features you need to discover, assess, prioritize and remediate vulnerabilities. Simple and efficient.
Automatic & Continuous
Every month, thousands of new vulnerabilities are discovered. New vulnerabilities are quickly identified through scheduled and continuous scanning.
Systematic & Proactive
Our platform is a great foundation for proactive cyber security defense through systematic and continuous efforts.
Risk-Based
Don’t get lost in all the data. Our platform helps you understand what vulnerabilities to remediate first through ransomware and exploits threat intelligence.
Automated Asset Discovery
We cover every asset in every environment and automatically discover new assets that are connected to our network.
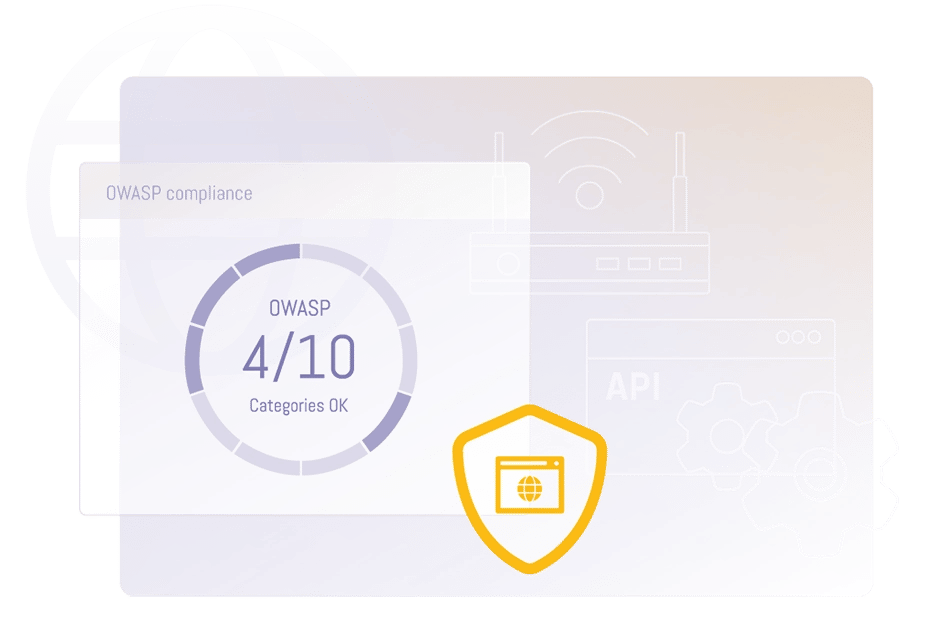
OWASP Top 10 & Much More
Our web application scanner finds a wide range of vulnerabilities, among others the OWASP Top 10. OWASP Top 10 is a widely recognized list of the top 10 most critical web application security risks compiled by the Open Web Application Security Project (OWASP). OWASP Top 10 covers vulnerabilities like injection, Cross-site scripting (XSS), and security misconfiguration.
Bring Critical Risks to the Forefront
Give your web applications the protection they need with our web application scanner. Our advanced technology detects a wide range of misconfigured and vulnerable web applications and APIs, automatically identifying web servers, programming languages, and databases. Ensure you're protected against the latest threats with Web Application Scanning.
Beyond OWASP Top 10
By discovering undocumented security vulnerabilities. Find SQL injections, vulnerabilities behind authentication, input sanitation problems, SSL and encryption misconfigurations, and more.
Continuous Scanning
Test your apps continuously for the latest vulnerabilities. Continuously monitors all of your web apps for vulnerabilities and misconfigurations with deep, authenticated scans.
How Can We Help You?
See the Difference a Next-Gen Vulnerability Management Platform Makes
From local government to industry-leading retailers, discover how Holm Security helps solve cyber security problems.
Cloud-based vs. On-Prem
Get Started In Hours - Fast & Powerful
Our Cloud-based deployment option is a comprehensive solution for automated and continuous vulnerability management with zero system requirements. It supports all sizes of organizations, all environments, and regardless of previous experience within Vulnerability Management. It only takes a few hours to get started with our powerful and easy-to-manage platform.
Best Choice for Data Privacy
Local data storage in your region and neutral company control. We provide the best choice for data privacy and data protection in the industry.
Public & Local Scanning
Our Cloud-based platform enables you to scan public systems as well as local infrastructure. Simple and powerful, giving comprehensive asset coverage.
For High-Security Demanding Organizations
Our On-prem deployment option is a comprehensive solution for automated and continuous vulnerability management that meets the demands of organizations that require high-security products, such as government organizations, the military, police, and secret service organizations.
Local Deployment - Local Storage
The platform is installed in your virtual environment supporting all common virtualization platforms. No data is communicated over the internet, meaning no data leaves your organization.
For High-Security Organizations
Our on-premise platform meets the demands of organizations that require high-security products, such as government organizations, the military, police, and secret service organizations.
FAQ
Here we answer the most frequent questions about Web Application Scanning.
What is Web Application Scanning?
Web Application Scanning is the process of automatically testing a web application for vulnerabilities. This is done by using specialized software that simulates attacks on the application in order to identify any vulnerabilities that could be exploited by attackers.
Web Application Scanning can be used to identify a wide range of vulnerabilities, including cross-site scripting (XSS), SQL injection, insecure file uploads, and insecure storage of sensitive data. By identifying and addressing these vulnerabilities, organizations can improve the security of their web applications and protect themselves from potential attacks.
Web application scanners typically work by sending requests to the web application and analyzing the responses for signs of vulnerabilities. They may also attempt to exploit known vulnerabilities in order to confirm their presence. Some web application scanners are designed to be run manually, while others can be configured to run automatically on a regular basis.
It is important for organizations to regularly scan their web applications for vulnerabilities, as this can help them to identify and fix potential security issues before they are exploited by attackers.
Do You Scan All Types of Web Applications?
Yes, we scan all types of web applications, such as commercial websites, intranets, portals, admin interfaces, and more.
Do You Scan for OWASP Top 10 Vulnerabilities?
Yes, we scan for OWASP top 10 vulnerabilities according to the latest version, 2021
Do You Support Authenticated Scanning?
Yes, we support both authenticated and unauthenticated scanning. With authenticated scanning, we scan the “inside” of your applications.
How Long Does It Take to Get Started?
It only takes a few hours to get started with our powerful and easy-to-manage platform. Contact us and we will help you get started today.
What Scan Technology is Used?
Our web application scanner is based on DAST (Dynamic Application Security Testing) and SCA (Software Composition Analysis). This means that we find vulnerabilities in the running application and in components used like WordPress and JavaScript libraries.
Is There any Software or Hardware Required?
If you choose the Holm Security cloud deployment option no 3rd party software or hardware is required. But for local scanning, you need to install one or multiple Scanner Appliances, which is a virtual appliance. If you choose to deploy on-premise you will need to install a minimum of two virtual instances. One core appliance and one Scanner Appliance.
How Do I Start Using Your Web App Scanner For My Web Security Testing?
You can start using our web app scanner by signing up for a demo account. Once you've signed up, you'll be able to log in to your account and start scanning your web applications. We also offer a free trial so that you can test out our product before committing to anything long-term.
How Long Time Does It Take to Perform a Web Application Security Test?
The length of time it takes to perform a web application security test depends on how large your application is and how many different types of tests need to be run against it. The more complex your site is, the longer it will take.
What is Static Application Security Testing?
Static Application Security Testing (SAST) is a security testing method that looks for software vulnerabilities. SAST does not test the software in action but analyzes the source code for potential vulnerabilities. This means that you can use SAST to find vulnerabilities in software that's already been deployed, and you don't need access to the production environment. Security issues like SQL Injection and Cross-Site Scripting (XSS) are common types of vulnerabilities found using static application security testing.
What is Dynamic Application Security Testing?
Dynamic application security testing (DAST) is a security testing method used to threat assess a web application while in runtime and identify any security vulnerabilities or weaknesses. Using DAST, a tester examines an application while it's working and attempts to attack it as a hacker would.
What integrations are available?
Latest News

DORA Decoded: Fusing Operational Resilience & Vulnerability Management
In this blog post, we're diving deep into DORA - why it's vital for digital service providers and financial institutions and why you should care about it.

Upgrade Your Cyber Defense To Comply With NIS2 - A Step-by-Step Guide On How To Prepare
This webinar will focus on the practical steps that IT departments need to take to improve their cybersecurity posture and adhere with NIS2 regulations.





