Secure your modern web applications using the latest technology
Assess all types of modern web applications for vulnerabilities.
Market-leading capabilities to secure your applications
Comprehensive assessment capabilities
Finding vulnerabilities like Cross Site Request Forgery (CSRF), Remote File Inclusion (RFI), as well as outdated JavaScript components, weak passwords, and web server and web framework misconfigurations.
OWASP Top 10 compliance
Find the most common web application vulnerabilities with the most powerful compliance framework.
Advanced authentication features
Supports a wide range of authentication methods for scanning web applications “behind” a login.
Modern web app support
Supports scanning of modern JavaScript-powered web applications using AI-driven threat intelligence.
Get the hacker's perspective
Determine how secure your organization is if cybercriminals attempt to hack your systems, target you with phishing attacks, or try to spread ransomware.
AI-driven threat intelligence
Our AI-powered Security Research team keeps you updated with the latest vulnerabilities – around the clock, all year round.
Supports the entire workflow
Our Security Center offers a single pane of glass for discovery, prioritization, remediation, and reporting.
Fully automated
Provides automated, continuous asset discovery and monitoring, vulnerability assessments, prioritization, reporting, and follow-up.
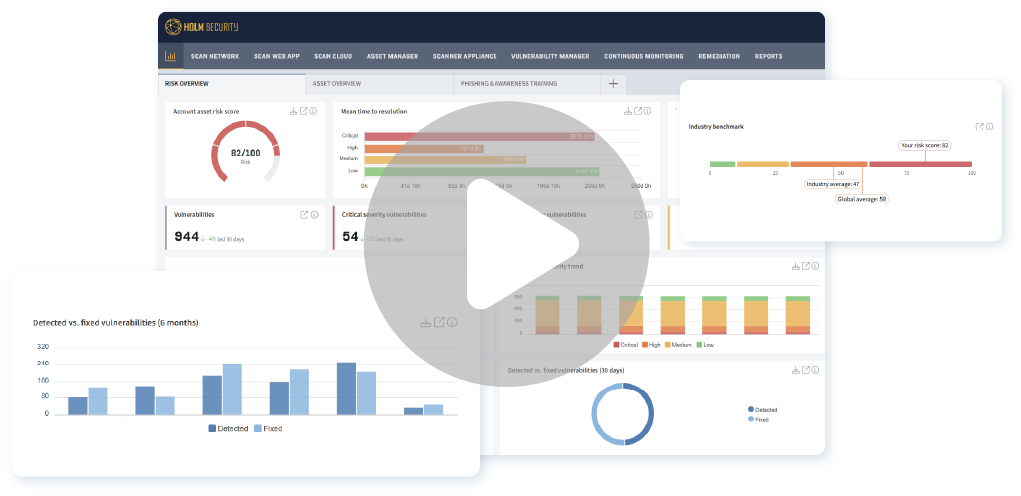
Watch our platform demo
Our market-leading platform is the cornerstone of a proactive cyber defense, empowering you to always stay one step ahead of cybercriminals.
Beyond OWASP Top 10 vulnerabilities
Full support for compliance assessments according to OWASP Top 10 versions 2017 and 2021 - and beyond.

SQL injection, XSS, CSRF, IDOR & much more
Find all common web application vulnerabilities such as SQL injection, Cross-Site Scripting, Cross-Site Request Forgery, Insecure, and Direct Object References.
Security misconfigurations
Identifies poorly configured web servers and web applications.
Outdated frameworks & components
Identify vulnerabilities in outdated programming languages and components, such as old PHP and JavaScript versions.
Sensitive data exposure
Misconfigurations exposing sensitive system information and sensitive data.
Weak passwords
Finds weak passwords used for authentication in all types of web applications – internal and internet-facing.
Web & domain blank spots
Continuous and automated asset discovery of web and domain assets with Attack Surface Management (ASM) and External Attack Surface Management (EASM).
Get started with a proactive cyber defense today
A growing number of web apps
What used to be desktop apps are today web apps. Accordingly, the risk exposure for web applications is growing rapidly. We find vulnerabilities in all types of web applications, both self-developed and commercial applications, such as commercial websites, specific web application systems, Intranets, portals and control panels, and admin interfaces.
The most powerful platform for compliance
Meet today's & future compliance
New legal requirements, directives, standards, recommendations, and certifications are continuously introduced in response to the growing threat landscape. We help you meet current and future requirements with a systematic, risk-based cyber defense, covering NIS, NIS2, DORA, CRA, GDPR, ISO 27001, and PCI DSS.

Integrated Attack Surface Management (ASM)
Web asset discovery
Automatically discovers, monitors, and continuously tracks web applications in your infrastructure with Attack Surface Management (ASM).
Domain asset discovery
Automatically discovers, monitors, and continuously tracks internet-facing domain assets with External Attack Surface Management (EASM).
Benchmark risk against industry peers

Efficiently measure & communicate risk
We provide all the tools you need to measure and communicate risks both internally and externally.
Benchmark your risk exposure
Gain insights into your organization's risk exposure compared to others in your industry.
A complete toolkit with Security Center
Discover
Automatically and continuously discover domain and web assets with Attack Surface Management (ASM) and External Attack Surface Management (EASM).
Assess
Automatically and continuously assess web applications.
Prioritize
AI-driven threat intelligence to guide your vulnerability prioritization.
Remediate
Full workflow support for remediation.
Streamline workflows with integrations
SIEM, ticketing, CMDB, CI/CD & more
Integrate vulnerability management into your routine workflow. We offer out-of-the-box integrations with a wide range of systems, including Security Information and Event Management (SIEM), Configuration Management Database (CMDB), patch management, ticketing systems, and Continuous Integration/Continuous Deployment (CI/CD).
Custom integrations
Using our Application Programming Interface (API), you can create custom integrations tailored to your specific needs.

All features and capabilities in Web Application Security
Cloud-based or on-prem
Get started in hours
Our cloud-based deployment option is a comprehensive solution for automated and continuous vulnerability management with no system requirements. It supports organizations of all sizes and environments, regardless of previous experience with vulnerability management. Getting started with our powerful and easy-to-manage platform only takes a few hours.
Best choice for data privacy
We provide the best choice for data privacy and data protection in the industry, with data processing and storage in a neutral country.
Public & local assessments
Our cloud-based platform enables you to scan both internet-facing systems and local infrastructure, providing you with a simple yet powerful solution with comprehensive asset coverage.
Full control over sensitive data
Our on-premise deployment option offers a comprehensive solution for automated and continuous vulnerability management designed to meet the needs of organizations that prefer to keep sensitive data within their own infrastructure.
Local deployment - local storage
Installed in your virtual environment, supporting all common virtualization platforms. No sensitive data is communicated over the Internet.
Unlimited scanners
Supports unlimited scanners, allowing you to scan your entire infrastructure, all managed through a single pane of glass for streamlined visibility.

















How can we help you?
Your trusted partner

Frequently asked questions
What is web application security?
Web application security is the process of automatically identifying vulnerabilities in web applications. As the number of web applications continues to grow, replacing traditional desktop and similar applications, the importance of web application security is increasing rapidly.
What type of web applications do you assess?
We scan all types of web applications, both self-developed and commercial applications, such as:
- Commercial websites
- Specific web application systems (custom-developed and standard)
- Intranets
- Portals and control panels
- Admin interfaces
Do you scan for OWASP Top 10 vulnerabilities?
Yes, we scan for OWASP Top 10 vulnerabilities according to the latest 2021 version. OWASP Top 10 is a globally respected compliance framework for securing web applications.
Do you support authenticated web application scanning?
Yes, we support both authenticated, where we scan the “inside” of your applications, and unauthenticated scanning. We support a wide range of advanced features for authenticated scanning.
What technology is used to do the assessments?
Our web application scanner is based on Dynamic Application Security Testing (DAST), and Software Composition Analysis (SCA). This means we identify vulnerabilities in the running applications and components used, such as JavaScript.
Is there any software or hardware required?
It depends on where the web application is deployed.
- Internet-facing web apps with cloud deployment: No software or hardware required.
- Local assessment using cloud or on-premise deployment: A virtual appliance scanner (Scanner Appliance) needs to be installed.
What is Dynamic Application Security Testing (DAST)?
Dynamic Application Security Testing (DAST) is a security testing method used to assess a web application during runtime, identifying potential security vulnerabilities or weaknesses. With DAST, testers examine the application in action, simulating attacks as a cybercriminal would. Holm Security leverages DAST technology to enhance web application security.
What integrations are available?
We provide many out-of-the-box integrations and integration possibilities using our platform API. Read more about integrations here.
